The Perimeter is Dead: Architecting a Zero-Trust Security Framework for the Indian Enterprise
For decades, enterprise security relied on a simple analogy: the castle and the moat. All critical data, applications, and users resided safely inside the corporate headquarters (the castle), protected by a robust perimeter firewall (the moat). If you were inside, you were trusted. If you were outside, you were blocked.
In 2025, that castle no longer exists.
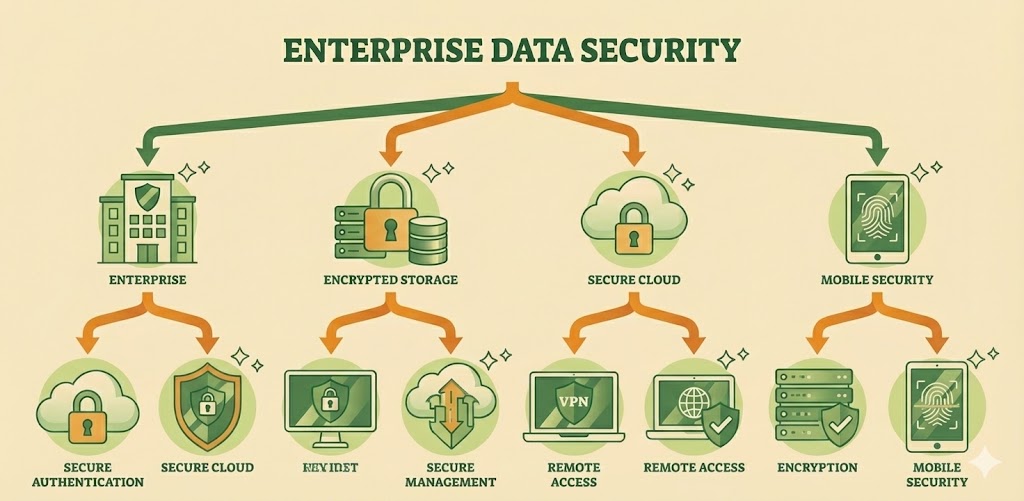
The rapid acceleration of hybrid work, the migration of workloads to multi-cloud environments, and the proliferation of IoT devices have dissolved the traditional network perimeter. Today, your users are everywhere, and your applications are hosted anywhere. In this distributed landscape, the assumption of "implied trust" is a critical vulnerability.
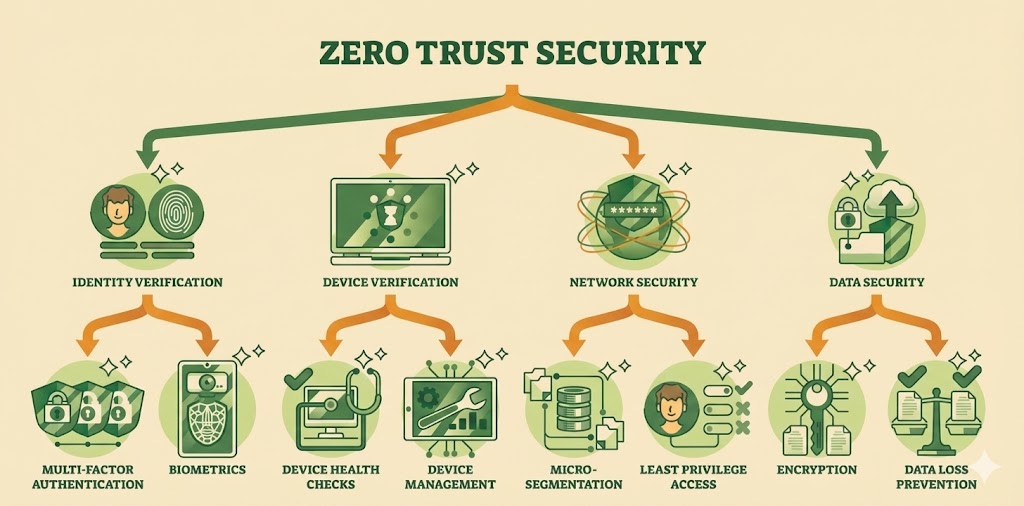
For IT leaders in mid-to-large scale enterprises, the mandate is clear: we must move from a perimeter-based security model to a Zero Trust Architecture. At Nexobots Technologies, we advocate for a security posture that operates on a single, uncompromising principle: Never Trust, Always Verify.
Research Your Destination
Before embarking on your journey, take the time to research your destination. This includes understanding the local culture, customs, and laws, as well as identifying top attractions, restaurants, and accommodations. Doing so will help you navigate your destination with confidence and avoid any cultural faux pas.
Lorem ipsum dolor sit amet, consectetur adipiscing elit, sed do eiusmod tempor incididunt ut labore et dolore magna aliqua. In hendrerit gravida rutrum quisque non tellus orci ac auctor. Mi ipsum faucibus vitae aliquet nec ullamcorper sit amet. Aenean euismod elementum nisi quis eleifend quam adipiscing vitae. Viverra adipiscing at in tellus.
Plan Your Itinerary
While it's essential to leave room for spontaneity and unexpected adventures, having a rough itinerary can help you make the most of your time and budget. Identify the must-see sights and experiences and prioritize them according to your interests and preferences. This will help you avoid overscheduling and ensure that you have time to relax and enjoy your journey.
Vitae sapien pellentesque habitant morbi tristique. Luctus venenatis lectus magna fringilla. Nec ullamcorper sit amet risus nullam eget felis. Tincidunt arcu non sodales neque sodales ut etiam sit amet.
Need IT network support? Let's connect Our team will get back to you with the right options.
Connect with Us
Pack Lightly and Smartly
Packing can be a daunting task, but with some careful planning and smart choices, you can pack light and efficiently. Start by making a packing list and sticking to it, focusing on versatile and comfortable clothing that can be mixed and matched. Invest in quality luggage and packing organizers to maximize space and minimize wrinkles.
Stay Safe and Healthy
Traveling can expose you to new environments and potential health risks, so it's crucial to take precautions to stay safe and healthy. This includes researching any required vaccinations or medications, staying hydrated, washing your hands frequently, and using sunscreen and insect repellent. It's also essential to keep your valuables safe and secure and to be aware of your surroundings at all times.
Immerse Yourself in the Local Culture
One of the most rewarding aspects of traveling is immersing yourself in the local culture and customs. This includes trying local cuisine, attending cultural events and festivals, and interacting with locals. Learning a few phrases in the local language can also go a long way in making connections and showing respect.
The Core Philosophy: Identity is the New Perimeter
In a Zero Trust framework, locality guarantees nothing. Being connected to the office LAN via an Ethernet cable should grant no more implicit access than connecting from a coffee shop Wi-Fi.
This shift requires a fundamental re-architecture of how Indian enterprises approach access control. Security must move from the network edge to the Identity and the Endpoint.
1. Explicit Verification
Every access request—whether from a C-level executive or a junior developer—must be fully authenticated, authorized, and encrypted. This goes beyond simple passwords. It requires Multi-Factor Authentication (MFA) and continuous validation of the user's context:
- Is the device managed and compliant?
- Is the location consistent with user behavior?
- Is the request occurring during standard business hours?
2. Least Privilege Access
The era of "flat networks" is over. Users should only have access to the specific resources they need to do their jobs, and nothing more. If a marketing manager's laptop is compromised, the attacker should not be able to laterally move into the finance server. This concept, known as Micro-segmentation, limits the "blast radius" of any potential breach, ensuring that a single vulnerability does not become a systemic catastrophe.
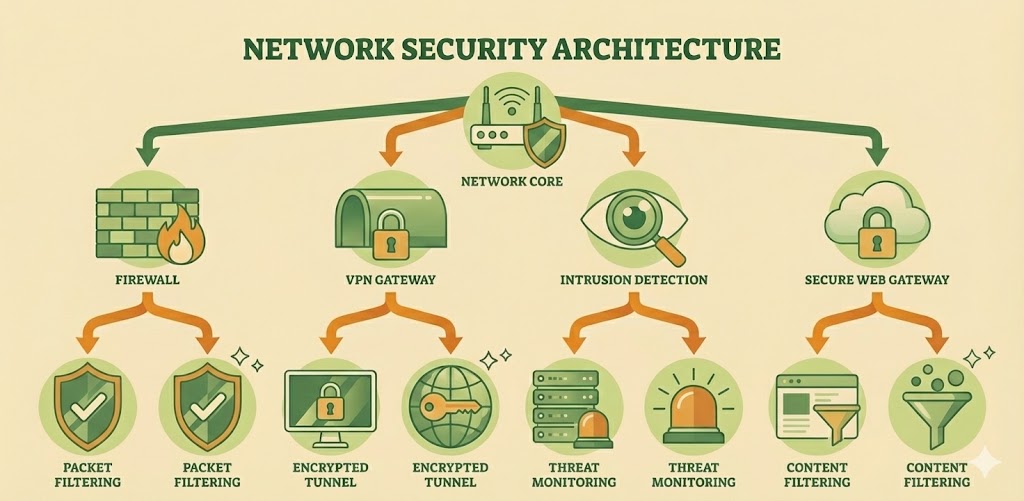
The Enforcer: Next-Generation Firewalls (NGFW)
While the perimeter has dissolved, the firewall has not become obsolete—it has evolved. The legacy packet-filtering firewall is insufficient for modern threats that hide within legitimate traffic.
A robust security posture relies on Next-Generation Firewalls (NGFW) from leaders like Fortinet, Palo Alto, and Cisco. These devices act as the enforcement engines of the Zero Trust policy, providing deep visibility that goes far beyond IP addresses and ports.
1. Deep Packet Inspection (DPI)
Modern malware is sophisticated; it often encrypts itself to bypass detection. An NGFW inspects the actual payload of the packet, not just the header. By decrypting traffic in real-time (SSL/TLS inspection), the firewall can identify and block ransomware, viruses, and malicious scripts hiding inside seemingly safe web traffic.
2. Intrusion Prevention Systems (IPS)
Security must be proactive. Integrated IPS capabilities allow the network to detect anomalous behavior patterns—such as a sudden spike in database queries or scanning attempts—and block the source IP immediately. This automates the defense against brute-force attacks and known vulnerability exploits.
3. Application Awareness
IT administrators need to control what is happening, not just who is connecting. NGFWs provide application-level control, allowing organizations to permit "Skype for Business" while blocking "BitTorrent," or allowing "Facebook" for marketing teams while blocking "Facebook Games." This granular control optimizes bandwidth and reduces the attack surface.
Securing the Hybrid Connectivity: SASE and VPN
With a workforce distributed across 180+ cities or working from home, secure remote access is non-negotiable. The traditional VPN concentrator often creates a bottleneck, backhauling all traffic to the HQ just to send it out to the internet.
The modern approach integrates security into the connectivity fabric itself—a concept often referred to as Secure Access Service Edge (SASE).
Split Tunneling with Security
Critical corporate traffic is routed securely via encrypted VPN tunnels to the data center, while benign internet traffic is routed locally but secured via cloud-based web gateways.
Endpoint Compliance
Before a remote device is allowed to connect to the VPN, the system checks its health status. Does it have the latest antivirus definitions? Is the OS patched? If not, the device is quarantined.
The Human Element: Biometric Integration
In a Zero Trust world, the "Who" matters more than the "Where." Passwords are the weakest link in the security chain. Integrating Biometric Authentication into the access control framework adds an irrefutable layer of identity verification.
Whether through fingerprint scanners for physical server room access or facial recognition for workstation login, biometrics bind the digital credential to the physical human. This eliminates credential sharing and significantly reduces the risk of identity theft.
The Watchtower: Managed Security and Threat Mitigation
Even the most advanced hardware cannot think. A firewall can block a packet, but it cannot analyze the strategic intent of a persistent attacker.
This is where the Managed Security Service Provider (MSSP) model becomes essential. Security is a 24/7/365 operation. A dedicated Security Operations Center (SOC) provides the human intelligence required to interpret the signals generated by the hardware.
Threat Hunting
Proactively searching logs for subtle indicators of compromise that automated tools might miss.
Incident Response
When a breach is attempted, speed is critical. A managed security team can isolate infected endpoints and revoke user credentials within minutes, preventing data exfiltration.
Conclusion: Security as a Business Enabler
For too long, security was viewed as a roadblock—the department of "No." In the modern Indian enterprise, security is a business enabler. A robust Zero Trust framework allows you to hire talent from anywhere, adopt any cloud service, and innovate faster than the competition, safe in the knowledge that your data—your organization's oxygen—is protected.
At Nexobots Technologies, we do not just sell firewalls; we architect resilience. By combining certified expertise across multi-vendor security platforms with a deep understanding of network infrastructure, we help enterprises build a security posture that is as dynamic as their business.
The perimeter may be dead, but your security has never been more alive.
About Nexobots Technologies
Nexobots is a premier provider of IT Infrastructure and Security Solutions. With Certified Multi-Vendor Expertise and a Pan-India support network, we empower enterprises to build secure, high-performance, and compliant digital ecosystems.